IDAM Strategy and Roadmap Consulting


IDAM / IGA
IDAM Strategy and Roadmap Consulting
At Borderless CS, we pride ourselves as the Leading IDAM consultancy in Australia, dedicated to empowering organizations with cutting-edge solutions. IDAM stands for Identity and Access Management, which refers to organisations' policies, procedures, and technologies to manage digital identities and control access to resources within their IT environments. Our IDAM strategy and roadmap consulting service are designed to assist businesses in developing a comprehensive plan for managing identities and access effectively across their systems, applications, and data.
We are committed to fortifying your organization's security posture, optimizing operational efficiency, and enhancing user experiences by implementing state-of-the-art identity and access management practices. Our tailored solutions are designed to not only mitigate security risks but also to streamline processes, ensuring seamless access to resources while safeguarding sensitive data. With our expertise, your organization can navigate the intricate terrain of digital identity management with confidence and ease. Partner with Borderless CS to unlock the full potential of your identity and access management strategy, and pave the way for a secure and efficient digital future.
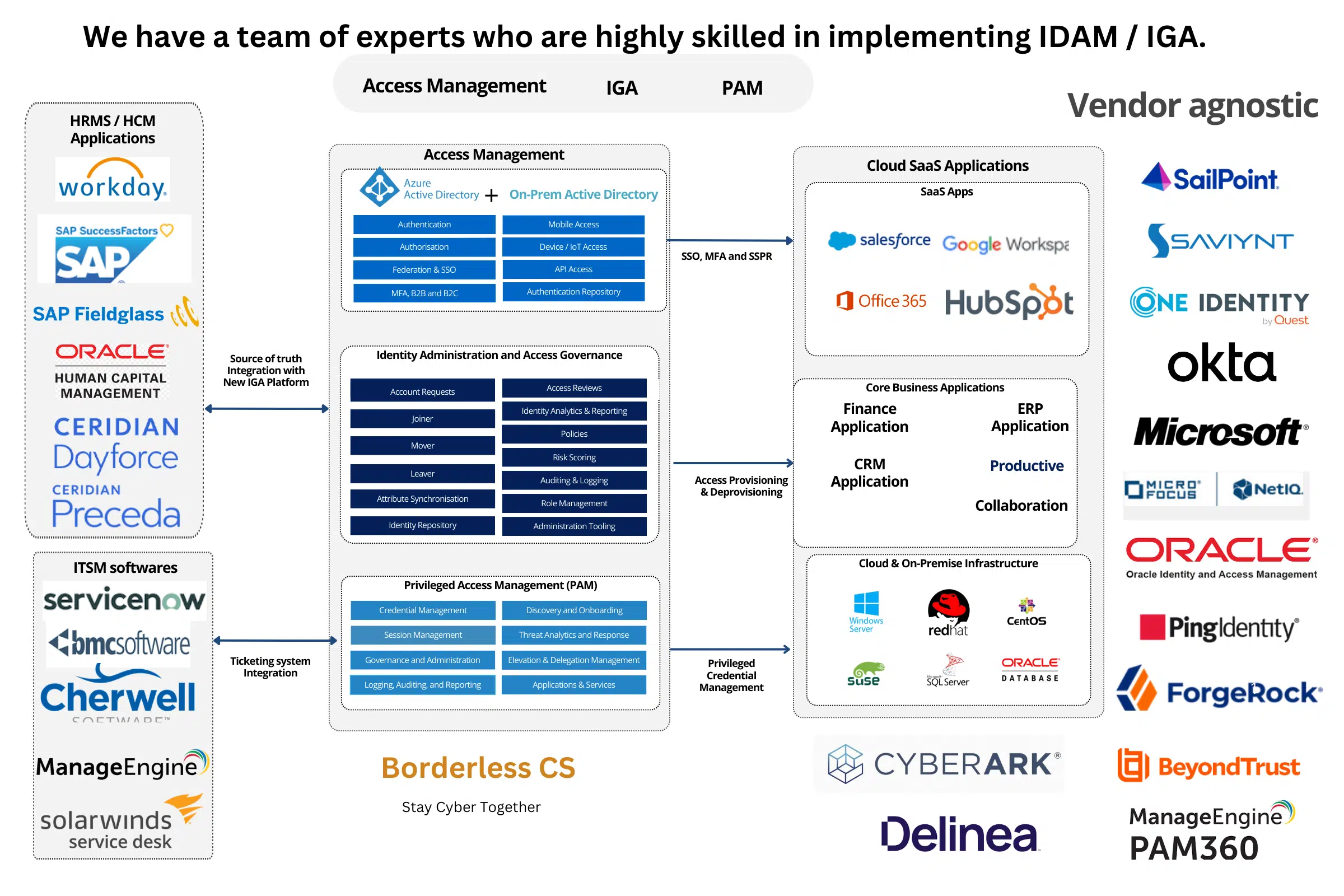
Access Management | Identity Administration and Access Goverance | Privileged Access Management
IDAM Strategy and Roadmap
Phase 1 : Assessment and Analysis:
We will begin by evaluating your organization's current state of identity and access management. This assessment will involve reviewing the current processes, technologies, and policies to identify areas for improvement and strengths.
Phase 2: Stakeholder Engagement:
Engage with key stakeholders across your organisation, including IT teams, security professionals, business leaders, and end-users. Understand their requirements, concerns, and priorities for identity and access management.
Phase 3: Strategy Development:
Based on the assessment and stakeholder input, We would work with your organization to develop a tailored IDAM strategy. This strategy would outline the vision, goals, objectives, and key initiatives for improving identity and access management practices.
Phase 4: Roadmap Creation:
- Develop a detailed roadmap that outlines the specific steps and milestones needed to implement the IDAM strategy successfully. This roadmap typically includes timelines, resource requirements, and dependencies for each initiative.
Phase 5: Technology Evaluation and Selection:
- Helping the organisation evaluate and select the right mix of technologies and solutions to support its IDAM strategy. This might involve assessing different vendors, products, and deployment options based on the organisation's requirements and budget.
Phase 6: Implementation Support:
- Providing support and guidance during the implementation phase ensures that the IDAM initiatives are executed effectively and according to plan. This might involve assisting with configuration, integration, testing, and rollout activities.
Phase 7: Training and Change Management:
- Developing training programs and change management strategies to help employees adapt to new IDAM processes, tools, and policies. This might include user awareness sessions, technical training for IT staff, and communication plans to keep stakeholders informed throughout the implementation.